
Three Chinese Digital Economy Policies at Stake in the U.S.ŌĆōChina Talks
Defining 'critical information infrastructure,' regulating cross-border data flows, and hints of an opening in cloud services
The U.S.ŌĆōChina economic confrontation has never been entirely about trade and tariffs. While U.S. negotiators have consistently sought market access in key tech sectors and lower barriers to cross-border business operations, their Chinese counterparts have long tried to exclude structural issues around digital trade from negotiations, claiming they touch on national security.
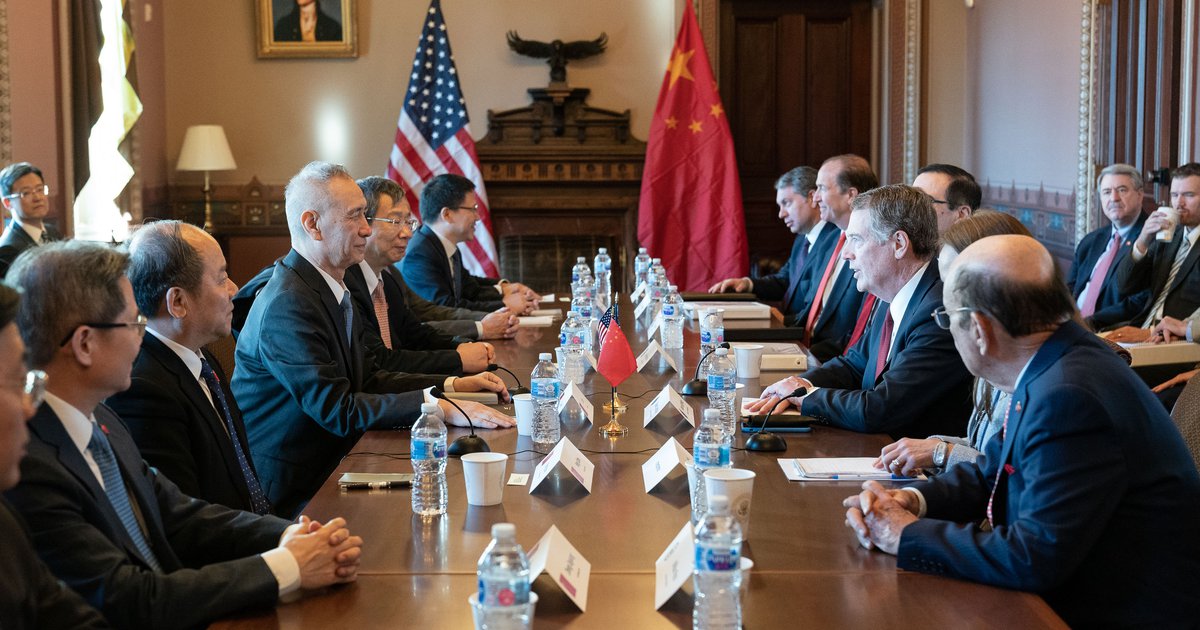
That resistance may now be eroding. ChinaŌĆÖs top negotiator, Vice Premier Liu He, is in Washington this week for further negotiations, and the Wall Street JournalŌĆÖs Lingling Wei and Bob Davis that ŌĆ£issues related to Chinese regulations of information security and cross-border data flows, as well as high-tech sectors such as cloud computing, crowded the negotiation agendaŌĆØ at the last round of talks last week.
Central to Chinese policy in these areas are the Cybersecurity Law (see DigiChina translation), which went into effect in June 2017, and an array of related regulations that shape the digital economy and generate concern among foreign businesses.
While the core provisions of the Cybersecurity Law are unlikely to be substantially amended or rolled back, important regulatory documents have not yet been finalized, giving negotiators grounds for a potential deal.
Below are three key digital policy areas at issue in the ongoing U.S.ŌĆōChina negotiations, accompanied by background analysis and translations DigiChina has produced since 2017.
1) How China defines ŌĆścritical information infrastructureŌĆÖ (CII) determines the reach of some of its most burdensome regulations.
Some of the provisions of the Cybersecurity Law that most concern foreign firms impose requirements on entities described as ŌĆ£critical information infrastructureŌĆØ (CII). According to the law, CII operators may only use network products and services that have undergone a national security review process (a so-called ŌĆ£black boxŌĆØ review that involves third-party organizations for which formal procedures do not yet exist). Organizations designated as CII operators must subject data they transfer out of China to a security review, and they must store certain data within mainland China. CII operators are also subject to security procedures like spot-testing and regular assessments.
The Chinese government, however, has not yet specified which sectors and organizations qualify as CII, so a wide range of businesses, both foreign and domestic, have been waiting since mid-2017 for certainty about their compliance obligations.
The Cybersecurity Law provides only the scaffolding of a definition, referring to CII as systems that ŌĆ£if destroyed, suffering a loss of function, or experiencing leakage of dataŌĆömight seriously endanger national security, national welfare, the peopleŌĆÖs livelihood, or the public interest.ŌĆØ A from July 2017 provided more specifics, clarifying that CII would include traditional sectors such as energy, finance, transportation, as well as other sectors such as social media and e-commerce that hold large amounts of personal data and which also fit the ŌĆ£seriously endangerŌĆØ description above.
The scope of CII, and therefore the reach of regulatory obligations that apply to CII, has been a major concern and lobbying point for foreign trade groups and industry since 2017. In the months after the Cybersecurity Law entered into force, senior Cybersecurity Administration of China (CAC) officials met regularly with U.S. industry and government representatives to discuss best practices for regulating critical infrastructure. Senior CAC officials at various times have assured foreign industry groups that they would work toward a narrow definition of CII. Until recently, however, CAC officials did not appear to be following through in response to foreign government and industry feedback.
WhatŌĆÖs new?
The Wall Street Journal last week that Chinese officials may be considering a definition that takes market share into account, potentially lessening regulatory burdens on smaller players in industries that otherwise would qualify as CII. Important uncertainties remain, however: the specifics of any newly proposed definition of CII are not clear; there is no guarantee CII will be part of any eventual deal; and, of course, the two sides may simply fail to reach an agreement at all.
Any resolution to the CII definition, meanwhile, would only partially address concerns about the reach and shape of regulations. The Cybersecurity Law not only outlines new regulations for CIIŌĆöthe ŌĆ£black boxŌĆØ review, data handling requirements, etc.ŌĆöbut also says CII and other entities are subject to a pre-existing cybersecurity regulation system known as the multi-level protection scheme (MLPS). That system operates under a different set of regulatory documents that are themselves currently under revision, with a new version known as MLPS 2.0 in . This situation is emblematic of the overlapping jurisdictions of the Ministry of Public Security (MPS, which operates MLPS) and the CAC (which oversees most other CII-related matters)ŌĆöa dynamic that any U.S.ŌĆōChina agreement would likely have to at least begin to address.
DigiChina coverage of critical information infrastructure:
- ChinaŌĆÖs Ambitious Rules to Secure ŌĆśCritical Information Infrastructure,ŌĆÖ July 14, 2017
- , July 10, 2017
- ChinaŌĆÖs Cybersecurity Law One Year On, November 30, 2017
(On the broader framework into which CII fits, including overlap with the MLPS.) - Progress, Pauses, and Power Shifts in ChinaŌĆÖs Cybersecurity Law Regime, July 18, 2018
(Noting that national security reviews for CII products and services are set forth in and that a CAC official in November 2017 hinted at a narrow definition for CII; and taking stock of a potential turf war between MPS and CAC.)
2) What limits will there be for companies moving data across borders?
Another limitation the Cybersecurity Law applies to CII operators is a requirement to store ŌĆ£personal information or important dataŌĆØ gathered or produced during operations in China within the country, and to only transfer such data abroad following a ŌĆ£security assessment.ŌĆØ
Businesses in general, Chinese or otherwise, view requirements for data localization or extra procedures for cross-border data transfer as logistical challenges or sources of extra cost. The U.S. government position in general has been to favor free flows of information across borders. The Cybersecurity LawŌĆÖs language on domestic storage and outbound data transfer security assessments have raised the specter of draconian data policies, although the worst fears have not yet come to pass.
Like the definition of CII, the procedures for the security assessment required for outbound data transfers are set out in documents that remain in draft form. Two documents ŌĆ£measuresŌĆØ and ŌĆ£guidelinesŌĆØ for the assessments, have been circulating since 2017 without being finalized.
U.S. officials at the negotiating table have been pushing the Chinese side to commit to allow more kinds of commercial data to be exported without undergoing a security audit. ItŌĆÖs not just foreign pressure agitating for a more narrow set of requirements. Debate within China on the issue has included spirited advocacy by Chinese domestic firms that rely on cross-border data flows for their own global ambitions.
WhatŌĆÖs new?
There is a possibility that Chinese negotiators would agree to allow certain kinds of commercial data to be exported without reviewŌĆöthereby giving U.S. negotiators something that looks like a ŌĆ£win.ŌĆØ But the scope of any such apparent concession would be crucial, since the result could be that large swaths of data deemed to be vital to national security remain tightly controlled.
Significant uncertainty remains within China as to the definition of ŌĆ£important data,ŌĆØ one of the categories that triggers the outbound data transfer assessment requirement in the Cybersecurity Law. According to stakeholders involved, this is likely to be addressed in the next major piece of the Cybersecurity Law framework to come out this year. To be meaningful, any U.S.ŌĆōChina understanding would need to be reflected in these yet-to-come regulatory documents moving forward.
DigiChina coverage of cross-border data transfer issues:
- Beyond the Worst-Case Assumptions on ChinaŌĆÖs Cybersecurity Law, October 13, 2017
Noting significant internal debate about how to implement Cybersecurity Law language on cross-border data transfers, including a translation of a pertinent Chinese government statement responding to a U.S. action at the World Trade Organization.
3) Cloud services could partially shed joint operation requirements, but ŌĆśpilotŌĆÖ or ŌĆśfree trade zoneŌĆÖ approaches may not satisfy U.S. demands.
The WSJŌĆÖs Wei that Premier Li Keqiang floated a proposal to authorize trial operations for foreign cloud service providers in a designated free-trade zone (FTZ). Under the proposal, foreign companies would be allowed to own the data centers, compared with current requirements to team up with local partners.
The details of how such a pilot program would work are unclear, but LiŌĆÖs remarks indicate the Chinese government is attempting to show that it is serious about addressing U.S. concerns over restrictions on U.S. cloud services providers. Cloud companies may still face onerous licensing requirements, and the WSJ reported that Li emphasized the need to ensure ŌĆ£privacy protectionŌĆØ for Chinese customers, raising the crucial questions: how would Chinese citizen data be treated, and what of how much if any exemptions from provisions of the Cybersecurity Law may come with operation in an FTZ?.
Moreover, it is not clear from reports on the initial proposal which types of companies would be eligible for such a pilotŌĆöfor example traditional cloud services providers, multinational telecommunications carriers, or other companies with a heavy cloud business presence.
Precedents and parallels
In January the licenses to BT that appear to be the first cloud computing licences awarded to a major western telecom firm. MIIT provided a BT China Communications Limited with a nationwide domestic IP-VPN license and a nationwide domestic ISP license, which significantly does not authorize mobile phone service or content providing service. This type of arrangement appears to be intended to allow BT to provide some services to multinational clients within China.
Now, in the context of the trade talks, something more expansive may be afoot. Opening to cloud services within certain limitations, starting in one or more FTZs, could be part of a gradual opening, but to be a major step it would need to go beyond allowing foreign firms to provide services to western companies operating in China.
There is precedent for this kind of partial or trial opening. Chinese regulators have allowed wholly foreign-owned enterprises (WFOEs) to operate online e-commerce platforms within the Shanghai FTZ and serve customers across China. The Shanghai FTZ experience, however, has been a limited one for foreign firms.
Conclusion
Almost two years after the Cybersecurity Law went into effect, and even longer since it was released in final form, ChinaŌĆÖs government continues to juggle competing interests in the bureaucracy, among Chinese and international businesses, and in pursuing security and economic goals.
ChinaŌĆÖs digital economy regulatory regime remains one of the worldŌĆÖs most comprehensive in design, but it is far from complete. If some long-standing questions are resolved as part of a U.S.ŌĆōChina economic understanding, more will surely remain.
Any U.S.ŌĆōChina deal would be a starting point. In 2015, U.S., European, and Japanese lobbying seemed to succeed in convincing the Chinese government to suspend a banking regulation requiring purchase of Chinese-sourced IT products under the logic that they were ŌĆ£secure and controllableŌĆØŌĆöbut that logic made its return in an array of rules and standards, including in the regime around the Cybersecurity Law, and including some of the policies now targeted by U.S. negotiators. Reporting suggests that U.S. negotiators are seeking long-term assurance of Chinese adherence to any deal by maintaining the threat of tariffs or other measures.





