In early 2014, while manually digging through data logs, one of the cyber analysts at my company noticed some suspicious activity on one of our client’s laptop. This particular device was active at a time of day when we knew it should have been idle — at this point, the customer support team had a baseline of the client’s device and network traffic and knew what was “normal” or abnormal. The volume of traffic looked innocuous, but the frequency was suspicious: The same event log had occurred at the exact same time each day for the past two weeks, suggesting that this was being caused by an automated script making regular connections to its command and control server. We ultimately determined this was, in fact, a malicious program hiding on the client’s device attempting to exfiltrate data. But the corporate cyber intrusion detection system we had in place at the client’s home never picked this up. It was our analyst who pieced this together.
This was hardly the first time that a human found something a system overlooked. That’s in part because at that time, as we were discovering the importance of humans to the work of cybersecurity, we were also learning that the cyber solutions that worked for big corporations just didn’t work for our client base of high-net worth individuals and families. Changes that could indicate a security threat for an individual are usually disregarded as mere noise by corporate systems that are built to monitor thousands of people.
But as individuals increasingly become targeted, it’s become critical to think differently about how we design cybersecurity systems. For us, that’s meant putting people at the center of everything we do, because humans are at the center of cyber crimes. Cyber criminals have figured out that hacking a human is easier than hacking the tech — and the end payouts are just as lucrative. We’ve seen, for instance, an explosive rise in wire transfer fraud and financial theft enabled through manipulating and deceiving people via email.
But as individuals increasingly become targeted, it’s become critical to think differently about how we design cybersecurity systems.
Here’s a true story of how it happened, from one of my clients (before he became a client). He was a retired executive living in the Midwest whose email account was hacked. The hackers sifted through his inbox and sent folder to learn about past communications and transactions with his banker, discovering his usual protocol for initiating wire transfers, what language he used, how he signed messages, etc.. Using that information, the cyber criminals crafted a convincing email to the banker from the executive’s account, asking for $700,000 to be transferred. The criminals also knew that, upon receiving the email, the banker would call the client to get verbal authorization for the wire. So, before hitting send on the email, they called the client’s phone provider, which they also found from old emails. Pretending to be the client, they asked to forward all calls to their number and provided all the necessary personal info to make changes on the account. Then when the banker did the call-back (which he did) the cybercriminal answered and pretended to be the client, authorizing the wire. A day or so later the client realized he hadn’t been receiving any calls or texts, and started to unravel what had happened.
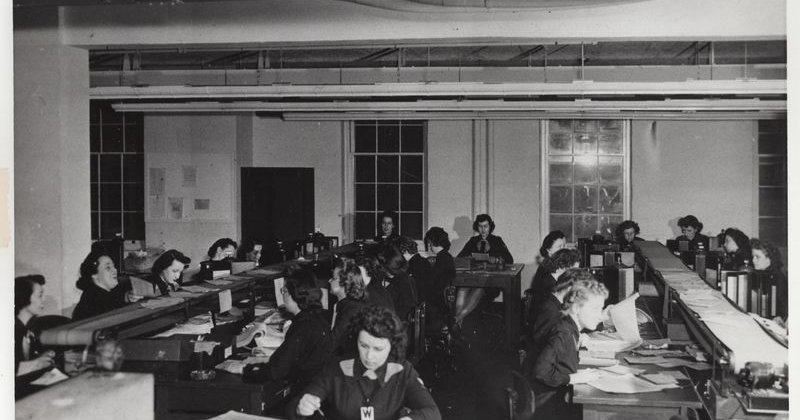
Cybercriminals are always looking for new ways to get to our data, our money, our devices. Every time we come up with a technical fix, they will find a new vulnerability, a new way in — even advanced tools like A.I. and machine-learning systems are no silver bullet. There are human criminals behind every cyber breach increasingly targeting people on the other side. And so there must be humans on defense — complementing the technological solutions. At Rubica, our edge — our ability to adapt, think outside the box, and stay ahead of the bad guys — is our people. A key factor in this is the diversity of our team. Diversity of perspective breeds innovation, creative problem-solving and better outcomes. By purposefully designing a work environment that’s inclusive, fosters creativity, and rewards proactiveness, we can see new dimensions of possibility (for both problems and solutions) and avoid blind-spots bred by homogeneous group-think.
Naturally, we’ll continue to deploy the most advanced tech and tools available. But our main cyber security investment will be in people.