I. Defining Vulnerability
Cybersecurity Vulnerabilities
refers to the system of practices, technologies, and policies used to protect data, devices, and users against , and other cyber harms. A cybersecurity ŌĆ£vulnerabilityŌĆØ is a weakness or gap that can be exploited; a cybersecurity ŌĆ£threatŌĆØ refers to malicious actors attempting to gain unauthorized access by exploiting a vulnerability; and a ŌĆ£riskŌĆØ is the potential loss or damage that results from a threat exploiting a vulnerability. A threat may be due to malware or to the ŌĆ£human factorŌĆØ (the general understanding that people will make mistakes).1 According to a 2025 Verizon report, 60 percent of all security breaches include some sort of human error (such as weak passwords, privilege misuse, or social engineering).2 Threats or risks may also be due to social engineering (tricking someone to reveal information), phishing attempts (fake emails or messages that contain malware), or viruses.
For the purposes of this report, human vulnerabilities in the context of cybersecurity should be more precisely defined as a subcategory of cybersecurity vulnerabilities that is not limited to technical systems or networks. These human-centered weaknesses (beyond being prone to mistakes or errors) are often the very entry points that are exploited. Accordingly, this report will highlight this subcategory when referring to the phrase ŌĆ£cybersecurity vulnerabilities,ŌĆØ but will retain the two different phrases (ŌĆ£human vulnerabilitiesŌĆØ and ŌĆ£cybersecurity vulnerabilitiesŌĆØ) to clearly articulate the bridge being built in this report between digital divide and cybersecurity policy.
Human Vulnerabilities
Although there are disciplines that study the impact of technology on people, or how someone who is vulnerable may be susceptible to certain risks, the definition of vulnerability used here is grounded in feminist and feminist legal theories.3 This choice is intentional: Feminist approaches treat vulnerability not as personal weakness but as a universal and structurally produced condition. By adopting this lens, the analysis shifts from individual blame and instead focuses on how systems create and perpetuate unequal exposures to harm. The result is a more critical examination of the vulnerabilities digital users face, and keener insights into how they might be addressed and eventually eliminated.
Martha Fineman, a leading scholar on critical legal and feminist legal theories and philosophies, describes vulnerability as both universal and situational.4 Essentially, everyone is vulnerable in some way, but their particular vulnerability hinges on the specific circumstances they face. This perspective shifts the concept of vulnerability from a given status or identity. FinemanŌĆÖs definition instead emphasizes the relationship between individuals and the state, which she believes has a responsibility to protect those rendered vulnerable by specific conditions. This report agrees with Fineman: There is a particular role that the government should play for those who are made vulnerable in digital circumstances.
The digital circumstances most relevant to this report are related to digital access, digital literacy, and digital skills. ŌĆ£Digital accessŌĆØ refers simply to access to the internet and other digital tools or systems. For some communities, access is limited not just by infrastructure, but by affordability, language, or cultural barriers. For example, if an artificial intelligence (AI) tool that individuals must use in order to access government-administered services does not provide translation services in the language they are comfortable speaking, that individual cannot be said to have access to that system, even if they have internet access.
Digital access, skills, and literacy are components of what is commonly referred to as the digital divide. In the late 1990s, the digital divide was used to describe the digital ŌĆ£haves and have-nots.ŌĆØ5 This understanding of the digital divide guided policy efforts that persist to this day. In 1999, the National Telecommunications and Information Administration published Falling Through the Net, a report that defined the digital divide and provided data on the levels of access in the United States.6 Today, despite so many lacking the ability to adequately use technology (that is, those lacking literacy and skills), the term ŌĆ£digital divideŌĆØ is still primarily used to refer to broadband access.7 When this report uses the term, it is referring not just to access, but to digital skills and literacy as well. All three dimensions of the digital divide are framed here as human vulnerabilities, as they increase the risk of exposure to cybersecurity threats. Further, each dimension represents a distinct but interconnected barrier that can increase an individualŌĆÖs exposure to digital risk.
Digital literacy and skills are often used interchangeably, but there is an important distinction. ŌĆ£Digital literacyŌĆØ refers to oneŌĆÖs ability to effectively understand, navigate, and evaluate digital outputs. Outputs can be anything from the text of a website to an AI-generated image. As the American Library Association notes, digital literacy includes not just the ability to evaluate digital tools but also critical thinking and the ability to use, interpret, and locate information.8
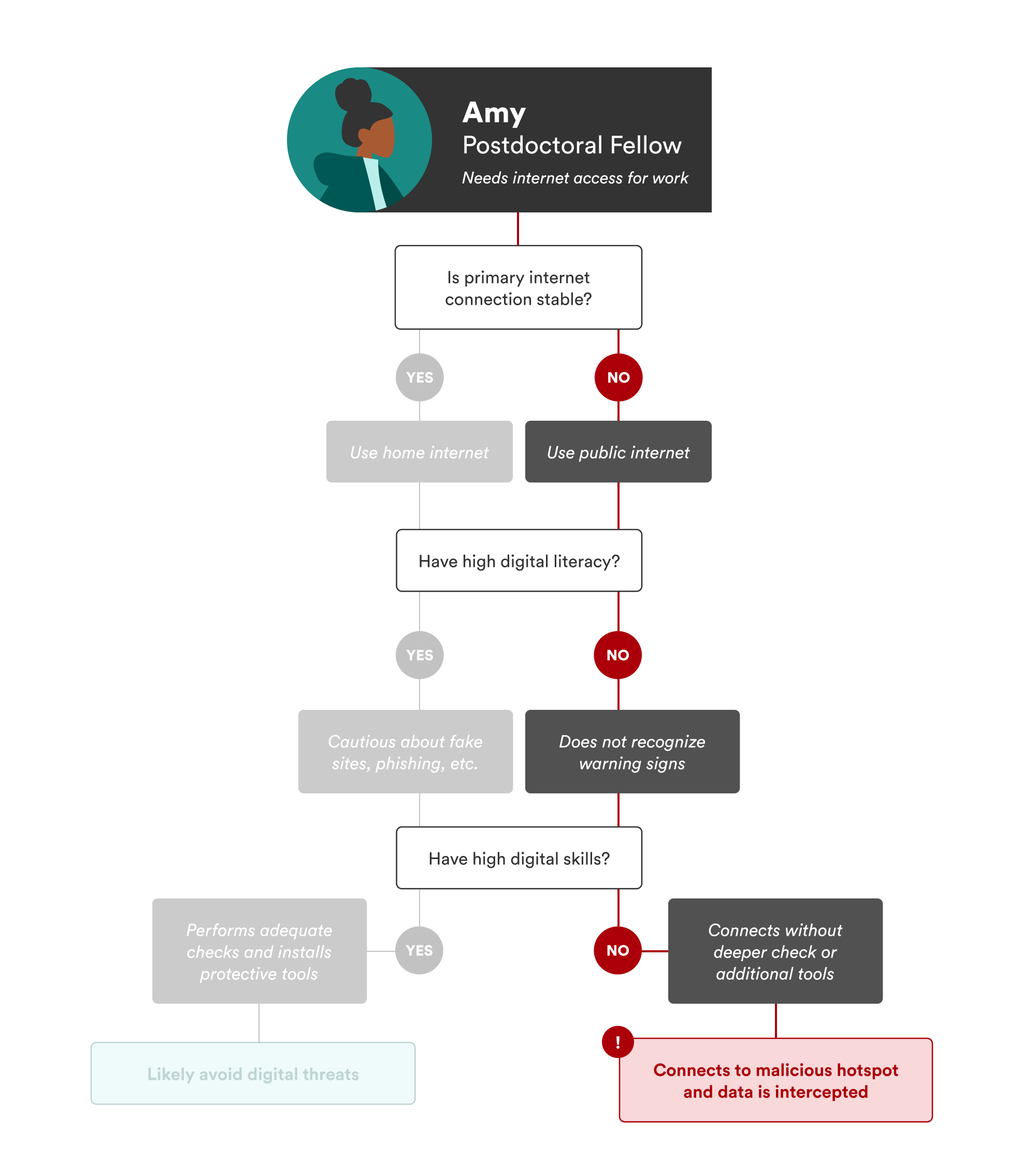
Relatedly, ŌĆ£digital skillsŌĆØ refer to the practical abilities one has to effectively engage with and use digital tools and systems. To differentiate between literacy and skills, consider a hypothetical student named Amy. Amy is a postdoctoral fellow living in affordable but poorly connected student housing. Her underground unit offers only spotty internet, forcing her to spend time at a caf├® across the street to reliably access the internet. Last week, Amy connected to what she thought was the caf├®ŌĆÖs Wi-Fi hotspot. After entering the usual password, she was taken to a screen she did not recognize. It claimed she was ŌĆ£logged in,ŌĆØ so she closed the screen. Unbeknownst to her, Amy had connected to a malicious hotspot with the same name as the caf├® network. Her data was quickly intercepted.
In this scenario, as illustrated in Figure 1 below, digital literacy might have helped her recognize something was amiss. International research indicates that individuals with stronger digital literacy tend to be more aware of security risks and engage in proactive behaviors to mitigate them.9 However, recognizing a risk does not automatically translate into action: Amy needed both digital literacy and skills. Digital skills would have enabled her to proactively investigate the network, adjust her security settings, and even install additional protections on her computer.
Thus, lacking sufficient digital literacy or skills, Amy became vulnerable to cybersecurity risks. In fact, her vulnerability began due to her lack of access: She would not have gone to the caf├® if she had had a reliable connection in her home.
Moving Away from Simplistic Labels
When discussing these vulnerabilities, it is important to move beyond surface-level labels and consider how structural conditions shape individual experiences. It may be easy to say that Amy was ŌĆ£vulnerableŌĆØ simply because she lacked digital access. More accurately, she was rendered vulnerable because of her situation, which is a critical distinction from labeling her as inherently or permanently vulnerable. Vulnerability is context dependent.
In an early comment on digital divide policy, digital librarian Steve Cisler cautioned against labeling people as digital haves or have-nots because it creates overly simplistic binary categories.10 At any given moment, one could be rendered vulnerable and become a digital have-not due to a specific situation, like a sudden lack of internet access or the inability to navigate a specific system, highlighting the fluidity of vulnerability. The label matters less than understanding the conditions that produced the vulnerability.
This critique of oversimplified labels highlights the importance of understanding feminist theories of vulnerabilities, such as Florencia LunaŌĆÖs concept of layered vulnerability. Luna argued that vulnerabilities should not be thought of as static traits but as layers that accumulate in specific contexts.11 This layered approach ultimately enables a more nuanced analysis.
Here, each situation that renders someone vulnerable adds a new layer that compounds risk or increases exposure. In AmyŌĆÖs case, her situation became more precarious not just because she lacked digital access (which could be considered her first layer of vulnerability), but because she also lacked digital literacy and skills (the second and third layers). Thus, affixing the label of ŌĆ£vulnerableŌĆØ to someone without access, literacy, or skills is not as useful as understanding vulnerability as a universal, context-dependent layered concept. It should be further noted how language is limiting in this situation: While it does make sense, here, to identify Amy as vulnerable due to her lack of access, skills, and literacy, policymakers should explore the hows and the whys of her specific vulnerabilities (in other words, the situation and the context), which can lead to more sophisticated, diverse solutions to addressing them.
Instead of saying, ŌĆ£Amy is digitally vulnerable. She needs X,ŌĆØ policymakers should explore how Amy is vulnerable and try to understand what she needs to address each layer of vulnerability, because ŌĆ£XŌĆØ alone may not be adequate. If ŌĆ£XŌĆØ were reliable internet connectivity (either in or outside her home), Amy would have digital accessŌĆöbut she still might lack digital literacy and skills to identify malicious or suspicious activity. In this case, ŌĆ£XŌĆØŌĆöinternet connectivityŌĆöwould only postpone her exposure to digital risk, not eliminate it. The push for understanding layers of vulnerability is important for this more thorough analysis.
Citations
- See Mark Evans et al., ŌĆ£Human Behaviour as an Aspect of Cybersecurity Assurance,ŌĆØ Security and Communication Networks 9, no. 17 (October 20, 2016): 4667ŌĆō79, ; Maher Alsharif, Shailendra Mishra, and Mohammed AlShehri, ŌĆ£Impact of Human Vulnerabilities on Cybersecurity,ŌĆØ Computer Systems Science and Engineering 40, no. 3 (September 24, 2022): 1153ŌĆō66, . Similar to the human factor is the concept of an insider threat, defined as ŌĆ£the potential for an insider to use their authorized access or understanding of an organization to harm that organization. This harm can include malicious, complacent, or unintentional acts that negatively affect the integrity, confidentiality, and availability of the organization, its data, personnel, or facilities.ŌĆØ ŌĆ£Defining Insider Threats,ŌĆØ Cybersecurity and Infrastructure Security Agency, . An insider threat, if the insider makes a mistake, could be considered the ŌĆ£human factor.ŌĆØ
- Verizon Data Breach Investigations team, 2025 Data Breach Investigations Report (Verizon Business, 2025), .
- See Daniella DiPaola and Ryan Calo, ŌĆ£Socio-Digital Vulnerability,ŌĆØ SSRN, January 17, 2024, ; Margret Hoehe and Florence Thibaut, ŌĆ£Going Digital: How Technology Use May Influence Human Brains and Behavior,ŌĆØ Dialogues in Clinical Neuroscience 22, no. 2 (2022): 93ŌĆō97, ; ŌĆ£Behavioral Indicators in Cybersecurity: A Comprehensive Guide,ŌĆØ SearchInform, . The susceptibility one has to certain risks is described in many disciplines, but this report references the discussion on vulnerability in the 2016 RAND cybersecurity framework. Igor Mikolic-Torreira, et al., A Framework for Exploring Cybersecurity Policy Options (RAND Corporation, 2016), .
- Martha Fineman, ŌĆ£The Vulnerable Subject: Anchoring Equality in the Human Condition,ŌĆØ Yale Journal of Law & Feminism 20, no. 1 (November 12, 2008): 1ŌĆō23, .
- Benjamin Remillard, ŌĆ£Access Alone IsnŌĆÖt Enough,ŌĆØ in Designing for Care, ed. Jerod Quinn, Martha Burtis, and Surita Jhangiani (Pressbooks, 2022).
- National Telecommunications and Information Administration (NTIA), Falling Through the Net: Defining the Digital Divide (NTIA, July 1999), .
- See ŌĆ£What Is the Digital Divide?,ŌĆØ Institute of Electrical and Electronics Engineers, ; ŌĆ£Closing the Digital Divide for the Millions of Americans Without Broadband Posted,ŌĆØ WatchBlog, General Accountability Office, February 1, 2023, ; Nicky Lauricella Coolberth, ŌĆ£The ŌĆśDigital DivideŌĆÖ Is ╣·▓·╩ėŲĄ Access to Devices and the InternetŌĆöBut ItŌĆÖs Also ╣·▓·╩ėŲĄ Access to Skills,ŌĆØ National Skills Coalition, September 15, 2021, .
- ŌĆ£Digital Literacy,ŌĆØ American Library Association, .
- See Musaddag Elrayah and Saima Jamil, ŌĆ£Impact of Digital Literacy and Online Privacy Concerns on Cybersecurity Behaviour: The Moderating Role of Cybersecurity Awareness,ŌĆØ Cyber Criminology 17, no. 2 (November 8, 2023): 166ŌĆō87, .
- Steve Cisler, ŌĆ£Subtract the Digital Divide,ŌĆØ San Jose Mercury News, January 15, 2000, archived at .
- Florencia Luna, ŌĆ£Elucidating the Concept of Vulnerability: Layers Not Labels,ŌĆØ Feminist Approaches to Bioethics 2, no. 1 (Spring 2009): 121ŌĆō39, .
