A Chapter of: The Digital Deciders
Two Poles and Three Clusters
It is tempting to romanticize Internet architecture and governance as innately embodying democratic values of equality, participatory openness, and multistakeholder oversight but there are several problems with this narrative. In a significant portion of the world, Internet governance control structures do not embody democratic values but involve systems of repression, media censorship, and totalitarian surveillance of citizens.1
– Laura DeNardis
Norms at the international level are likely to reflect actions at the national level around the globe. To that end, internet governance, as described by DeNardis above, is not one thing. It is a suite of issues including technical design standards, data retention and localization policies, and many things in between. Some of these issues should appropriately involve or even be driven by private stakeholdersÔÇöcivil society or industry. Others, though, still need to be driven by the state.
DeNardisÔÇÖ words ring just as true today as they did in 2014. Two loose models for the internet and its governance exist. On the one hand, a predominantly free and open internet driven by a multistakeholder governance model; on the other, a sovereign and controlled version of the internet, where the state exerts authority over the architecture, often in the name of some form of security, usually resulting in a censored or unfree space. These two models represent poles of attraction. In reality, national-level internet regimes exist on a spectrum between these two camps with fewÔÇöif anyÔÇöfully embodying the extremes of either camp.
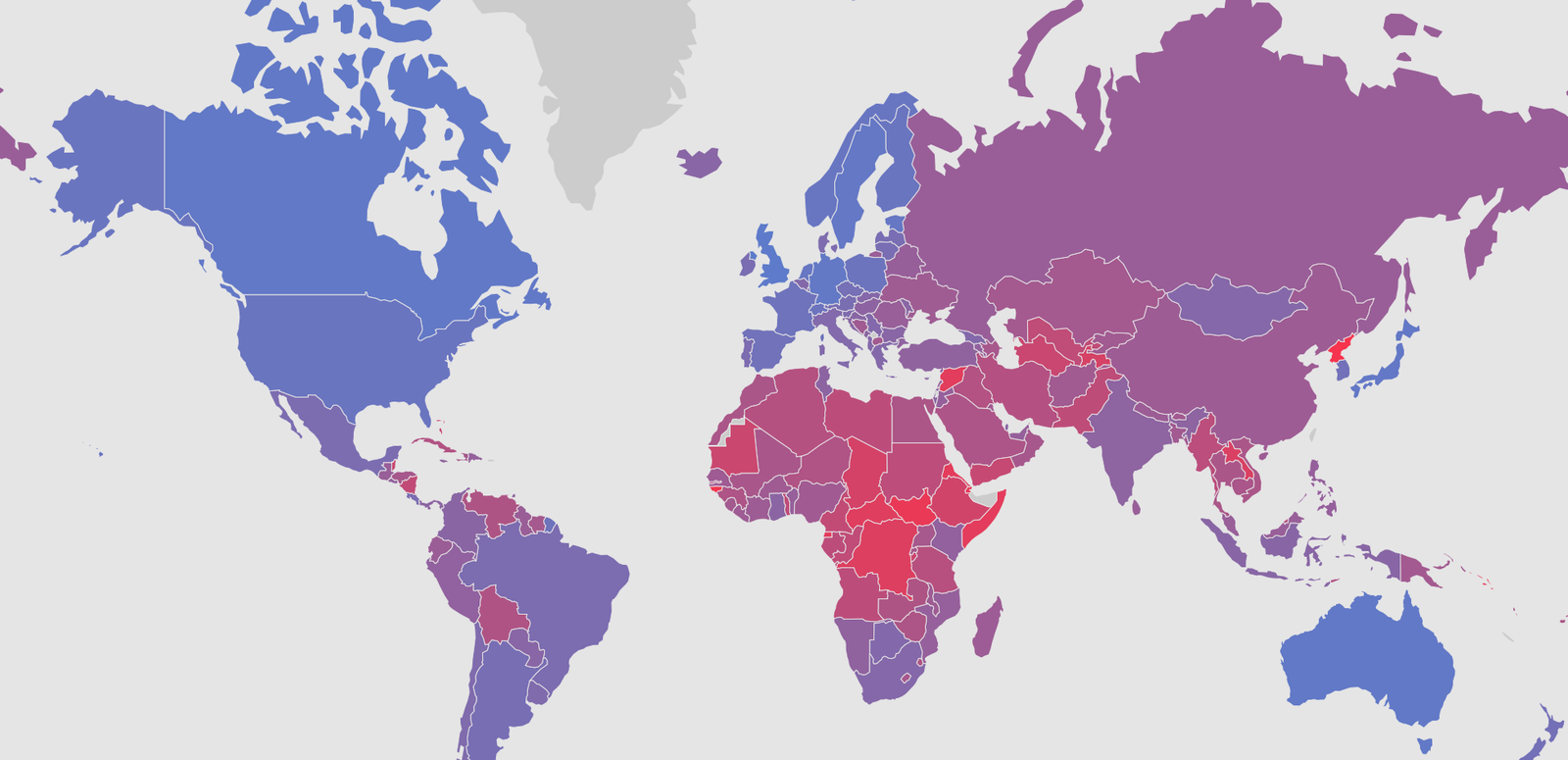
In order to depict this phenomenon, we use a simple plot consisting of two spectrums as the axes: one measuring internet openness and the other capturing the character of internet governance.
Openness means different things to different people. For the early internet pioneers, ÔÇ£openÔÇØ referred to the principle that internet architecture should be agnostic to the traffic on it. What this would mean, in practice, is that architecture would not discriminateÔÇöblock or throttleÔÇödifferent packets based on what was contained in them. However, openness in the political context has increasingly come to describe the content environment of a countryÔÇÖs internet. A fully open internet in this context refers to an internet absent of any censorship, throttling, or blockingÔÇöwhether of content or any other type of internet traffic. As authoritarian countries push to legitimize censorship and democrats laud the power of the internet for spreading democracy, it is this second version of openness that has been placed at the center of the internet governance debate. It is also this version of opennessÔÇöcontent opennessÔÇöthat we map on our x-axis. On the far right, we have a completely open internet. On the far left, we have an internet whose content is completely moderated.
The character of governance is the extent to which the state hasÔÇöor should haveÔÇöa monopoly over internet governance in its country and is mapped along the y-axis. Full monopolyÔÇöwhere the government is a solitary decision maker on internet governanceÔÇöis the bottom of the spectrum, whereas pure multistakeholderismÔÇöwhere each relevant stakeholder has a voice in governance decisionsÔÇöis the top of the spectrum. A country where the state has a monopoly over all internet policy decisions, can dictate architectural changes and configurations, and sets standards would fall on the bottom of the spectrum. A country where control is partially distributed would fall near the middle of the spectrum. A country where control is equitably distributed would sit at the top of the spectrum.
The poles of attractionÔÇösovereign and controlled and open and globalÔÇöare the bottom left and top right of the graph, respectively.
The exercise of plotting countries on these spectrums reveals a clear differentiation between two clusters of countries, with a few countries sprinkled throughout the middle. In the lower left-hand corner is a cluster of states that take a heavy-handed approach to governing the internet and tightly control the content on that internet. The opposing cluster is slightly less well defined. Looking at the far right end of the plot we see a series of countries that generally favor an open internet, but their governance model is less starkly defined. In addition, the 2014 and present day comparison reveals that this second cluster of countries (on the far right end of the spectrum) have begun to creep closer and closer to the middleÔÇöa visual depiction of the challenges to the multistakeholder and open models we previously described.
No longer do the camps only represent models for global internet governance. Instead, these two camps represent distinctÔÇöbut seemingly compatibleÔÇömodels for the internet itself.
This plot depicts the steady consolidation of states into two clusters, one in the Sovereign and Controlled quadrant of the graph and the other in the Global and Open quadrant, over the last four years. With this consolidation comes greater clarity of the impact of these models on the functioning of the internet. No longer do the camps only represent models for global internet governance. Instead, these two camps represent distinctÔÇöbut seemingly compatibleÔÇömodels for the internet itself: one placing freedom and opportunity for individual users front and center, the other emphasizing sovereign control and managing threats to political stability. Yet, so long as interconnection continues to workÔÇöthat is, filtering and blocking happens at the borders of national networksÔÇöthese models may not break one another.
That these two clusters exist is not groundbreaking. What matters is where these clusters plotÔÇöthe general trend down and to the left in our scatterplotÔÇöand where countries that do not yet fit into either of these clusters reside in relation to each cluster. To better understand these dynamics, let us first explore the principles and practices of each cluster.
Sovereign and Controlled
Whoever masters the Internet holds the initiative of the era, and whoever does not take the Internet seriously will be cast aside by the times.2
– Zhuang Rongwen, Chief of the Cyberspace Administration of China
In September 2018, newly appointed chief of the Cyberspace Administration of China (CAC), Zhuang Rongwen, published an essay outlining the Communist Party of ChinaÔÇÖs plan to ÔÇ£exert full control over the information flowing over ChinaÔÇÖs portion of the Internet,ÔÇØ according to a translation by DigiChina.3 For Zhuang, ÔÇ£Whoever masters the Internet holds the initiative of the era, and whoever does not take the Internet seriously will be cast aside by the times.ÔÇØ4 While some of the means proposed by Zhuang in his essay were novel, the end was not. This notion, that the state must master the internet to stay relevant, has been present in parts of the world for the better part of two decades.
This approach was embodied at the international level first in 2011 when a group of countries, including China, Russia, and several Central Asian Republics submitted a letter to the United Nations General Assembly (UNGA). The letter, which was resubmitted in 2014 with minor changes, opined on ÔÇ£the need to prevent the potential use of information and communication technologies for purposes that are inconsistent with the objectives of maintaining international stability and security and may adversely affect the integrity of the infrastructure within States, to the detriment of their securityÔÇØ and sought to reaffirm ÔÇ£that policy authority for Internet-related public issues is the sovereign right of States, which have rights and responsibilities for international Internet-related public policy issues.ÔÇØ5 In short, as early as 2011, governments in Russia, China, and a group of allies sought to legitimize a consolidation of sovereign control over the internet through international institutions.
So what does this approach look like in practice? For the better part of five decades, the creators and stewards of the internet have expounded on the benefits of its statelessnessÔÇödescribing a solitary internet as challenging territorial borders, needing its own law and legal institutions.6 The Sovereign and Controlled approach challenges these notions, placing ÔÇ£more authority in the hands of the state,ÔÇØ and viewing ÔÇ£cyber activity as occurring within the jurisdiction of these states, rather than within a stateless data environment.ÔÇØ7 As Jack Margolin notes, for Russia at least, the sovereign approach to the digital space mirrors ÔÇ£the KremlinÔÇÖs conception of ÔÇÿsovereign democracy,ÔÇÖ a term used to justify RussiaÔÇÖs right to eschew certain democratic principles in the name of ÔÇÿstabilityÔÇÖ and sovereignty in its own affairs.ÔÇØ Cyber-sovereignty challenges an ÔÇ£internationalist approach to norms of digital governance.ÔÇØ8 For China, arguably the leader of this pack, ÔÇ£Cybersecurity and informatization are a single body with two wings, the two wheels of a single drive, and require unified planning, unified deployment, unified promotion, and unified implementation.ÔÇØ9 While there is some variation between Sovereign and Controlled approaches, the model manifests with a number of generalizable traits with regard to governance process and character, as well asÔÇöparticularlyÔÇöinternet openness.
As early as 2011, governments in Russia, China, and a group of allies sought to legitimize a consolidation of sovereign control over the internet through international institutions.
First, with regard to governance process and character the cluster of states that have gravitated towards the Sovereign and Controlled end of the spectrum tend towards a statist approach to internet governance. In contrast to the popular multistakeholder governance movement from the mid-2010s, this statist approach to internet governance grants the state outsizedÔÇöif not completeÔÇödecision-making power over governance. Crucially, internet governance impacts the internetÔÇÖs architecture as well as the policies guiding corporations, developers, and users. Decision-making power may come via state-owned and operated corporations, public infrastructure, laws and regulations that legitimize state direction of private corporations, quiet agreements, or simple intimidation.
Second, these countries tend to favor a more closed version of the internet. Through legal and technical means as well as social norms and intimidation, the market for information on the internet is strictly controlled by the state. In China, this means the continued iteration on the Golden Shield project, which uses technical and human means to manipulate the Chinese internetÔÇÖs architecture to filter out content deemed malicious by the state.10 Similarly, the Iranian state is able to control the few physical points of ingress for the internet in Iran effectively enough to block information at the borders.11
In part because of the nature of its internet architecture, the Russian model for information control departs from these technical means of censorship and, in a sense, the flow of online information is freer. Rather than employing heavy-handed filtering of traffic, the Russian government deploys a system called the System for Operative Investigative Activities (SORM), which allows the government to intercept and view all traffic on their networks.12 The presence of this pervasive surveillance coupled with strict laws regarding legal and illegal information and communications achieves a similar censoring effect to that of the Chinese ÔÇ£Great FirewallÔÇØ or the Iranian ÔÇ£Halal NetÔÇØ.
In his book, The Darkening Web, Alex Klimburg aptly outlines the Sovereign and Controlled model and provides an assessment of some of its pitfalls. To Klimburg, the ÔÇ£core notion of cyber sovereignty is on its surface beguilingly simple: a state should be totally sovereign within its borders,ÔÇØ rendering it free from foreign influence or interference. According to Klimburg, this implicates both internet content in the country and the ÔÇ£logical and physical infrastructure on the local Internet segment,ÔÇØ what we refer to as the internetÔÇÖs architecture. Sovereignty in this space, to its champions, is meant to help states ÔÇ£better protect not only its citizens from bad content but also the critical infrastructure and government systems from hostile outside forces.ÔÇØ For this to work, contends Klimburg, the sovereignty of states must be ÔÇØimmutable and absolute,ÔÇØ and this is simply not the case.13 Compounding these fallacies is the notion that sovereign control over domestic internets could lead to breakdowns in the interconnection of the global network, impacting the way the internet acts and presents outside of those sovereign bordersÔÇöa somewhat paradoxical reality. If your sovereign internet inevitably interferes with the functioning of mine, are you respecting my sovereignty?
The Sovereign and Controlled cluster of states plot at the extreme ends of both of our described spectrums and appear clustered in the bottom left corner of Figure 1.
Global and Open (albeit without consensus on how)
Americans sometimes took for granted that the supremacy of the United States in the cyber domain would remain unchallenged, and that AmericaÔÇÖs vision for an open, interoperable, reliable, and secure Internet would inevitably become a reality. Americans believed the growth of the Internet would carry the universal aspirations for free expression and individual liberty around the world. Americans assumed the opportunities to expand communication, commerce, and free exchange of ideas would be self-evident.
– National Cyber Strategy of the United States of America, September 2018
On the opposite end of the spectrum of content control sits a cluster of countries that gravitate towards the global and open end of the content spectrum, but have been volatile with regard to governance structures. This is the cluster of states we wrote about in our Internet Ideals vs. Internet Realities report and consists of a group of like-minded states that favor a global internet that embodies principles of openness, freedom, interoperability, security, and resilience. As the 2018 U.S. National Cyber Strategy observes, many AmericansÔÇöand many of AmericaÔÇÖs alliesÔÇöÔÇØtook for granted that the supremacy of the United States in the cyber domain would remain unchallenged, and that AmericaÔÇÖs vision for an open, interoperable, reliable, and secure Internet would inevitably become a reality.ÔÇØ14 Likewise, this Global and Open cluster, spearheaded by U.S leadership, ÔÇ£believed the growth of the Internet would carry the universal aspirations for free expression and individual liberty around the world.ÔÇØ15
Within this cluster, there is a general consensus that a global internet is not only in the best interest of individual states, but in the best interest of the entire globe. Likewise, there is consensus that opennessÔÇöthough there is some contention over what that term meansÔÇöis in the national and global best interest. However, less consensus exists in how, exactly, to design both domestic and international governance structuresÔÇölaws, regulations, standards, and normsÔÇöto achieve this reality.
Within this cluster, there is a general consensus that a global internet is not only in the best interest of individual states, but in the best interest of the entire globe.
The American model for the internet was indeed embraced by many of the U.S.ÔÇÖ friends and allies. In 2017, the French strategy sought an internet driven by principles of ÔÇ£ouvertureÔÇØ (openness), ÔÇ£neutralite des reseauxÔÇØ (network neutrality), and ÔÇ£liberte dÔÇÖacces garantie par une architecture decentraliseeÔÇØ (freedom of access guaranteed by a decentralized architecture).16 The U.K. similarly calls for a ÔÇ£free, open, peaceful and secure cyberspace.ÔÇØ17 Thus, as with the Sovereign and Controlled cluster, the Global and Open share some generalizable characteristics.
Most notably, these countries favor internets that enable the free flow of internet content, freedom of speech, and global e-commerce. In the past, many of these countries soughtÔÇöat least in principleÔÇöto construct systems of internet governance that allotted governance power equitably to stakeholders, including government stakeholders, but also industry, academia, and civil society. At the same time, these countries sought to build internets that embodied the early internet principle of openness. What this meant in practice was that internet infrastructure would be designed and governed to treat all internet traffic equally, thereby not throttling or filtering any of the packets flowing through it.
However, in recent years, both the practicality of a pure multistakeholder system of internet governance and the desirability of the free flow of all data over global networks, have come into question. The governments of the U.K. and Israel are exploring ways to filter out certain malicious traffic at their borders. Data localization and other laws restricting internet content are becoming more commonplace.18 In addition, governments are increasingly intervening on their internetÔÇÖs architecture in order to bolster national cybersecurity. These interventions have the often unintended and unstated consequence of consolidating control and influence over the internetÔÇÖs architecture in the hands of states, leaving Milton Mueller to ask: ÔÇ£Is cybersecurity eating internet governance?ÔÇØ19 Yet, today this Global and Open cluster is stillÔÇöaccording to both doctrine and actionÔÇöin favor of a more open version of the internet, though the shape of this vision, the meaning of open, and the best governance structure to achieve it are all in flux.20 Indeed, as portrayed by the movement of this cluster towards a more statist and closed approach to the internetÔÇödown and to the left in Figure 1ÔÇöthe sovereign and controlled pole has some attraction.
The Global and Open cluster of states plots at the extreme end of the openness spectrum, but tends to be scattered between the middle and the equitable end of the governance spectrum. A sampling of Global and Open states plots in the top right quadrant of Figure 1, especially in the present day.
The Digital Deciders
I think the most likely scenario now is not a splintering, but rather a bifurcation into a Chinese-led internet and a non-Chinese internet led by America.21
– Eric Schmidt
Despite the attraction of these poles, not every state around the world possesses either the capacity or interest to pursue or commit to either model. Indeed, many states have not yet codified one model or the other, and some might even argue that, quietly, a third modelÔÇöone that cedes control over the internet to corporate actorsÔÇöhas emerged and is thriving in parts of the world. The "Digital Deciders" are those states that remain largely undecided and possess the capacity to influence the global conversation.
In part to avoid confusion in an era where election cybersecurity is a hot topic, we do not refer to this group as swing states, as we did in 2014. Nonetheless, in a one-state-one-vote context, as would be the format for the negotiation of a treaty at the UN, these states act much like swing states and we use similar criteria to isolate the Digital Deciders. According to Richard Fontaine, swing states in the American political context ÔÇ£are those whose mixed political orientation gives them a greater impact than their population or economic output might warrant.ÔÇØ22 In 2014, we defined a swing state in foreign policy as ÔÇ£a state whose mixed political orientation gives it a greater impact than its population or economic output might warrant and that has the resources that enable it to decisively influence the trajectory of an international process.ÔÇØ23 This reality means that states can take on new responsibilities, complicate solutions to significant challenges, or free-ride on established countriesÔÇÖ positions if they find alignment. In the context of internet governance and the internetÔÇÖs architecture, it is these Digital Deciders that will determine the prescience of SchmidtÔÇÖs projection.
Citations
- Laura DeNardis, The Global War for Internet Governance, (New Haven, CT: Yale University Press, 2014), 16.
- Rogier Creemers, Paul Triolo, and Graham Webster, ÔÇ£Translation: ChinaÔÇÖs new top Internet official lays out agenda for Party control online,ÔÇØ DigiChina – ╣·▓·╩ËãÁ, Sepbember 24, 2018, source.
- ibid.
- ibid.
- United Nations General Assembly, Letter Dated 9 January 2015 from the Permanent Representatives of China, Kazakhstan, Kyrgyzstan, the Russian Federation, Tajikistan and Uzbekistan to the United Nations addressed to the Secretary-General, 69th Session, Agenda item 91, January 13, 2015, Available at:
- See, for example: David Johnson and David Post, ÔÇ£Law And Borders-The Rise of Law in Cyberspace,ÔÇØ Stanford Law Review 48 (1996): 1367-1390.For a discussion on the fallacies of borderlessness, see: Jack Goldsmith and Tim Wu, Who Controls the Internet? Illusions of a Borderless World, (Oxford, UK: Oxford University Press, Inc., 2006).
- Jack Margolin. ÔÇ£Russia, China, and the Push for Digital Sovereignty,ÔÇØ Global Observatory, December 6, 2016, .
- ibid.
- Elsa Kania, Samm Sacks, Paul Triolo, and Graham Webster, ÔÇ£ChinaÔÇÖs Strategic Thinking on Building Power in Cyberspace, DigiChina – ╣·▓·╩ËãÁ, September 25, 2017, source.
- Pingp, The Great Firewall of China: Background, (Palo Alto, CA: Stanford University, 2011) .
- Collin Anderson, ÔÇ£How Iran is Building its Censorship-Friendly Domestic Internet,ÔÇØ WIRED, September 23, 2016, . And Collin Anderson and Karim Sadjadpour, IranÔÇÖs Cyber Threat (Washington, DC: Carnegie Endowment for International Peace, 2018), 39-48, .
- Andrei Soldatov and Irina Borogan, Inside the Red Web: The Struggle Between RussiaÔÇÖs Digital Dictators and the New Online Revolutionaries (New York, NY: PublicAffairs, 2015). See and excerpt from the book here: .
- Alexander Klimburg, The Darkening Web: The War for Cyberspace (New York, NY: Penguin Press, 2017) 110.
- The White House, National Cyber Strategy of the United States of America, September 2018, .
- ibid.
- Government of France, Strat├®gie Internationale de la France pour le Num├®rique (French International Digital Strategy), December 2017, 14, .
- Government of the United Kingdom, National Cyber Security Strategy 2016-2021, November 2016, 63, .
- William Alan Reinsch, ÔÇ£A Data Localization Free-for-All?ÔÇØ Center for Strategic & International Studies, March 9, 2018, .
- Milton Mueller, ÔÇ£Is cybersecurity eating internet governance? Causes and consequences of alternative framings,ÔÇØ Digital Policy, Regulation and Governance 19, no. 6 (2017): 415-428, .
- This trend is illustrated by the movement towards the center of every Open Internet country in Figure Figure 1 from 2014 to present day.
- Lora Kolodny, ÔÇ£Former Google CEO predicts the internet will split in twoÔÇöand one part will be led by China,ÔÇØ CNBC, September 20, 2018,
- Richard Fontaine and Daniel M. Kliman, ÔÇ£International Order and Global Swing States,ÔÇØ Washington Quarterly 36, no. 1 (2013): 93, .
- Tim Maurer and Robert Morgus, Tipping the Scale: An Analysis of Global Swing States in the Internet Governance Debate (Waterloo, Canada: The Centre for International Governance Innovation and the Royal Institute for International Affairs, 2014), .